
Cyber Security Testing
Build Resilience with Industry-Leading
Cybersecurity services
Cybersecurity testing plays a crucial role in ensuring the integrity of systems against evolving threats. It helps identify vulnerabilities, weaknesses, and potential entry points that malicious actors could exploit. Our services, facilitated by certified cybersecurity consultants, offer comprehensive testing methodologies tailored to meet diverse organizational needs.
Through thorough assessments, penetration testing, and vulnerability scans, we pinpoint vulnerabilities and recommend robust mitigation strategies to defenses. Additionally, our solutions prioritize non-repudiation, ensuring that actions or transactions cannot be denied by any involved party, thus meeting essential security requirements and bolstering trust in digital interactions.
Cyber Security Testing Challenges and Solutions

- Complex modern IT environments
- Evolving attack techniques and malware sophistication
- Shortage of skilled cybersecurity professionals
- Compatibility with legacy systems
- Regulatory compliance requirements
- Encryption of traffic and cloud-based services
- Tailored security testing solutions
- Penetration testing for early detection of vulnerabilities and potential threats
- Robust mitigation strategies suggested by certified cybersecurity consultants
- Vulnerability scanning to pinpoint weaknesses in applications and systems
- Managed security services for continuous monitoring, detection and response to cyber threats
- Integration of non-repudiation mechanisms to ensure trust in digital transactions
Business Benefits
Get In Touch- Certified Ethical Hackers
- Adherence to International Standards
- Zero False Positives
- Industry-leading tools
Our Security Testing Services
Our Security Testing Services offer an end-to-end suite of testing solutions to safeguard your digital assets. Our package of five different segments of Cybersecurity testing include:
Continuous Security
We provide continuous security through, DevSecOps, Continuous Compliance Monitoring, Continuous Cloud and Infra Security, Continuous Application Security, Security Analytics & Reporting.
Vulnerability Management
We identify, assess, prioritize, and mitigate security vulnerabilities in systems and applications through regular scanning, patching, and monitoring. This helps to protect against potential threats and minimize risks, ensuring overall security and integrity.
Cloud Security
Effective cloud security ensures the confidentiality, integrity, and availability of cloud-based resources. We protect data, applications, and infrastructure in cloud environments from threats. We implement access controls, encryption, monitoring, and compliance measures to safeguard against data breaches and cyberattacks.
Managed Security Operations Center
We provide threat detection, incident response, and round-the-clock security monitoring and management. With our advanced tools and expert analysts, we protect you protection against cyber threats, enhancing overall security and compliance.
Cyber Security Advisory and Consulting
We guide and protect against cyber threats through risk assessments, policy development, incident response planning, and compliance strategies. By leveraging specialized knowledge, we help businesses enhance their security posture, mitigate risks, and ensure robust protection of digital assets.
Our Clients
Speak to an expert
In your line of work, we know every minute matters.
Tx-Accelerators that boost Security
Tx-Secure
Tx-Secure is a unique security testing accelerator combining a specific set of processes and guidelines with tools and checklists to perform security checks. Tx-Secure:
- Helps perform red team, blue team, and purple team testing
- Test applications across web apps, mobile apps, Blockchain, IoT, Network, infra security, etc.
- Is in compliance with international standards such as GDPR, HIPAA, PCI-DSS, OSSTMM, OWASP, and others
Tx-DevSecOps
Tx-DevSecOps is a dynamic DevOps security accelerator offering a framework for continuous security testing and vulnerability management. Tx-DevSecOps:
- Enable digital businesses to optimize their application’s security within the existing DevOps CI/CD pipeline and ensures safer code deployment
- Embed security checks within the existing DevOps environment to track and remove modern threats and helps to deliver secure software
- Support the Continuous Integration DevOps Pipeline
- Deliver secure code adopting the shift-left approach to security testing
- Manage the Vulnerability life cycle efficiently

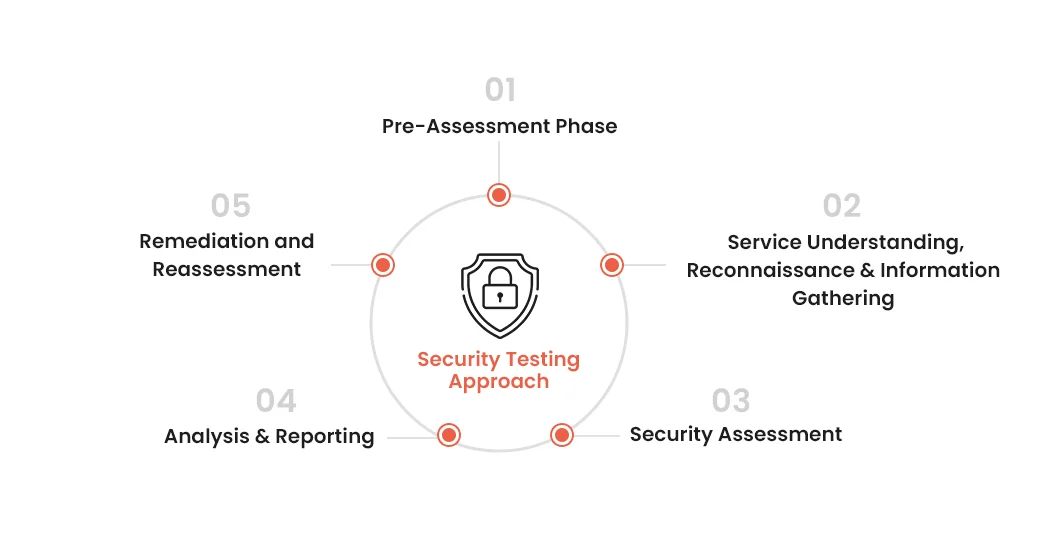
Our Approach
We follow a holistic approach to identify potential vulnerabilities in web apps, web services, and infrastructure by using the required tools and procedures.
Why choose Tx?
Our security testing practices adhere to international standards, including OWASP (Open Web Security Project) and OSSTMM (Open Source Security Testing Methodology Manual).
We offer vendor-independent security testing services and possess deep expertise in key security technologies.
We offer complete coverage of regression testing to safeguard against the introduction of new vulnerabilities.
Our iterative strategy aims to make applications vulnerability-free and secure for future releases
We utilize a range of industry-leading tools, including HP WebInspect, IBM AppScan, Acunetix, Cenzic Hailstorm, Burp Suite Pro, and various open-source tools, to enhance our security testing capabilities
100+ Certified Ethical Hackers who bring specialized expertise to our security testing efforts.




