In an increasingly interconnected world, the security landscape for small-to-medium-sized businesses (SMBs) or large enterprises — has grown more complex and fraught with potential cyber threats. It is no longer a question of if an attack will occur but when. This is where red team assessments, a proactive and dynamic approach to testing an organization’s defenses, come into play. Businesses that undergo red teaming can discover hidden attack paths and vulnerabilities that can become targets of social engineering tactics.
According to IBM, the average data breach could cost companies over $4 million, a significant impact of cyber incidents. Furthermore, a CISA study revealed that persistent access was unlocked to the targeted organization’s network during the red team exercise, highlighting the security gaps needing urgent attention. These assessments are a regular diagnosis and critical to making business IT infrastructure resilient against cyber threats.
What is Red Teaming?
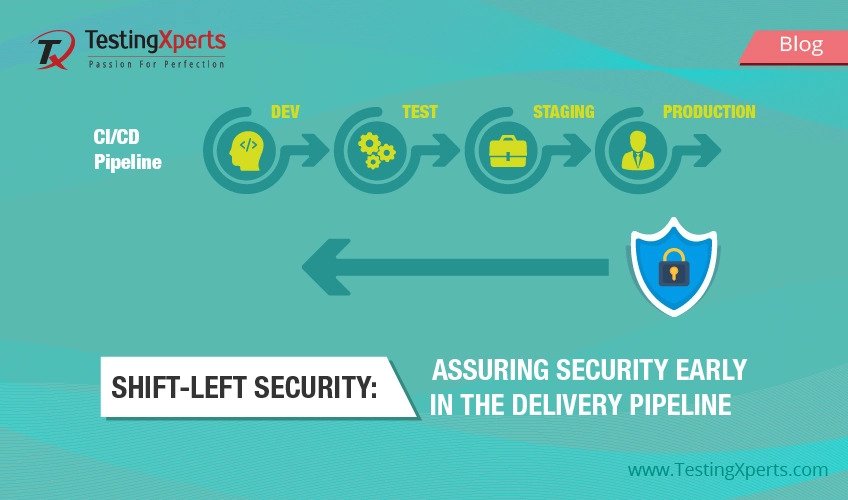
Red Teaming is a form of ethical hacking in which a designated team (the Red Team) acts as adversaries to exploit weaknesses in a company’s cybersecurity defenses. Unlike standard vulnerability assessments or penetration test, Red Team Assessments are comprehensive, multi-layered attacks against an organization’s people, processes, and technology. The objective is to find vulnerabilities and see how well a company’s security posture matches a simulated attack under real-world conditions.

The process starts with planning and scoping to draft the assessment based on business-specific security requirements. Red teamers collect data (similar to real attackers) to draft possible attack scenarios. Then, they execute these attacks to test digital and physical security posters, including social engineering, targeting network vulnerabilities, and attempting physical security breaches. The primary goal is to find security gaps and test how well a business security infrastructure, including people, can withstand these attacks. Doing so gives insights into how well security measures would perform during real cyberattacks and will ultimately improve business detection and response strategies.
The Importance of Red Team Assessments
Understanding the effectiveness of their security measures against sophisticated attacks is crucial for businesses. Red team assessments provide a safe environment to test response protocols, identify security gaps, and improve incident response times. These exercises are critical for maintaining security and compliance with industry regulations and standards, which increasingly recognize the importance of proactive security measures. Following are some of the reasons why red teaming is necessary in the current digital business age.

• A 31% increase in cyberattacks has grown yearly, making businesses more vulnerable.
• 70% of SMBs do not have robust security protocols to face a single cyberattack.
• 72% of state and local governments globally attacked by ransomware had their data encrypted.
• 40% of CEOs said that hybrid business IT infrastructures were the most challenging aspects of cybersecurity to implement.
• 47% of healthcare breaches occurred due to third-party insiders, and insider threats caused 43% of security breaches.
Red teams validate the effectiveness of current security measures to determine whether security protocols are robust and followed by employees. These assessments enable businesses to stay one step ahead by identifying the impact of emerging cyber threats and testing how well their security protocols withstand them.
Red Team vs VAPT

| Aspect | Red Team Assessments | Vulnerability Assessment and Penetration Testing (VAPT) |
| Objective | Analyze business’s detection and response capabilities using multi-layered attack simulations. | Identify and exploit vulnerabilities in the system. |
| Scope | Broad and comprehensive, aiming to mimic real-world attacks across all assets. | Only focus on identifying specific vulnerabilities in the systems. |
| Approach | Follows a strategic approach focusing on understanding and exploiting business process vulnerabilities. | Follows technical approach, concentrating primarily on IT infrastructure and software vulnerabilities. |
| Duration | Longer duration to simulate extended attack scenarios that might occur over weeks or months. | Shorter engagements, typically lasting for a few days or weeks. |
| Complexity | Involves complex scenarios, including the combination of digital, physical, and social engineering attacks. | Involves technical scans and exploits without the physical and social engineering components. |
| Outcome | Offers realistic assessment of business’s readiness against cyber threats. | Delivers a snapshot of exploitable vulnerabilities at a specific point in time. |
| Team Involvement | A multi-disciplinary team of network security, physical security, and social engineering experts. | Involves cybersecurity experts focusing only on IT vulnerabilities. |
| Interaction with Staff | Usually includes interaction with the staff to test awareness and response to social engineering. | Limited interaction with staff and focus more on technical aspects. |
| Results Utilization | Used to enhance strategic security decisions, employee training, and overall security posture. | Used to patch and fix identified technical vulnerabilities. |
| Cost | It is usually expensive because multiple consultants are involved, and it involves extensive and comprehensive tests. | It is less expensive than red teams but only focuses on technical aspects. |
Benefits of Red Team Assessments
Red teaming have become a crucial aspect of implementing robust cybersecurity strategies. Hackers are always looking for new ways to exploit loopholes in business IT security protocols. By evaluating multiple attack patterns, businesses will have a more accurate insight into security posture. Following are some of the benefits of conducting red team assessments.
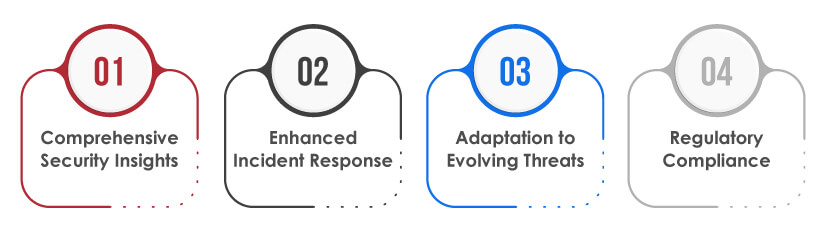
Comprehensive Security Insights
By emulating the behavior of potential attackers, red team assessments help organizations identify and reinforce weak points in their networks, applications, physical security, and even employee security awareness. They help build a stronger and more effective security posture against evolving cyberattacks.
Enhanced Incident Response
Regular red team assessments train internal security teams to respond more effectively to real cyber threats, reducing potential downtime and mitigating the risk of substantial financial and reputational damage. It allows teams to practice responding to an attack, upscale strategies, and improve cross-departmental communication to ensure effective action when facing real threats.
Adaptation to Evolving Threats
The cybersecurity landscape continuously evolves, with attackers constantly developing new methods. Red teaming allows organizations to stay ahead of these threats by regularly updating defense mechanisms against the latest attack vectors.
Regulatory Compliance
Many industries have strict regulatory requirements for cybersecurity. Regular red teaming can help ensure compliance, avoid penalties, and maintain customer trust by demonstrating a commitment to security.
Summary
In conclusion, red teaming is essential to a robust cybersecurity strategy, particularly for organizations that handle sensitive data or operate in high-stakes environments. At Tx, we are committed to empowering SMBs and large enterprises with the insights and tools they need to defend against and mitigate the impacts of cyberattacks. Investing in such proactive security measures is not just about protection—it’s about ensuring continuity, maintaining customer trust, and fostering a resilient business environment.
How Tx Enhances Red Team Assessment Outcomes?
At Tx, we specialize in providing Red Team Assessments that mimic real-world adversaries’ tactics, techniques, and procedures (TTPs) to help businesses bolster their cybersecurity defenses. We don’t just implement red teaming; we tailor them to each client’s needs and threat landscapes. Here’s how we ensure maximum coverage and results.

Customized Attack Simulations
Depending on the client’s industry, size, and specific security concerns, we develop bespoke Red Team strategies that target the most relevant and critical areas of their business.
Expert Team
Our red team comprises industry experts with extensive experience in cybersecurity, including former military cyber warfare experts and private sector cybersecurity specialists. This depth of experience ensures that our assessments provide real-world attack simulations.
Integrated Technologies
We leverage state-of-the-art technology and intelligence gathering to simulate the most advanced adversaries. The latest cybersecurity research and real-time global cyber threat intelligence inform our approach.
Actionable Insights
After the assessment, we provide detailed reports and debriefings highlighting vulnerabilities and offering practical, prioritized recommendations for strengthening systems and training personnel.
Continuous Improvement
Security is not a one-time event but a continuous process. We support our clients in evolving their security posture with ongoing assessments and updates to security strategies based on the latest threats.
For more information on how Tx can help your organization stay ahead of cyber threats with tailored Red Team Assessments, visit our website or contact our security consultants today. Together, we can build a cybersecurity strategy that defends, adapts, and thrives in the face of cyber challenges.
Discover more
Get in Touch
Stay Updated
Subscribe for more info