Today’s businesses are trying to cope with the adverse effects of the COVID-19 pandemic, while a wave of cyberattacks continues to pose a challenge for businesses. These cyber-threats significantly increased during the COVID-19 pandemic as employees worked from home. Due to this new work culture, many vulnerabilities surfaced online that weakened the security of systems, networks, and data, across organizations worldwide.
- An overview of cyber security
- Significant cyberattacks
- Why do businesses need to adopt cyber security measures?
- How can businesses protect themselves from cyberattacks?
- What is the need for outsourcing cyber security testing?
- Benefits of outsourcing your cyber security testing include
- How to choose your outsourcing partner for cyber security testing?
- Conclusion
- How can TestingXperts help?
Apart from the remote working culture, other reasons for the sudden increase in cyberattacks include weak passwords, public internet usage, unprotected systems/networks, and downloads from unknown sources, etc. Some of the most common attacks include Phishing, Ransomware, Password Attack, Cross-site Scripting, SQL Injection, Malware, DOS, Zero-day Exploit, etc. Eventually, today, it has become essential for all businesses to protect their critical apps, systems, data, and networks from cyber threats by adopting cyber security measures.
An overview of cyber security

Cyber security, also known as information technology security, protects computers, networks, servers, applications/software, data, and more from cyberattacks. Its main aim is to combat cyber threats and protect businesses from any form of vulnerability. Cyber security is categorized into five types: critical Infrastructure Security, Application Security, Network Security, Cloud Security, and Internet of Things (IoT) Security.
Significant cyberattacks

According to The Stack, on 04th Feb 2022, The UK Foreign Office was hacked in a major cybersecurity incident, forcing it to parachute into additional support with “extreme urgency” from its cybersecurity contractor BAE Systems Applied Intelligence. The UK government only revealed the existence of the “serious cyber security incident” affecting the Foreign, Commonwealth, and Development Office (FCDO) through a public tender announcement.
According to AP News, a series of cyberattacks on 15th Feb 2022 knocked the websites of the Ukrainian army, the defense ministry, and major banks offline. In such attacks, websites are barraged with a flood of junk data packets, rendering them unreachable. As per the report, at least 10 Ukrainian websites were unreachable due to the attacks, including the defense, foreign, and culture ministries and Ukraine’s two largest state banks.
Forbes, in one of their article on ‘More alarming cybersecurity stats for 2021,’ states that Americans seem to be wakening up to the need for better cybersecurity. A poll by The Pearson Institute and The Associated Press-NORC Center for Public Affairs Research shows that “about 9 in 10 Americans are at least somewhat concerned about hacking that involves their personal information, financial institutions, government agencies or certain
According to a report published by IBM, titled ‘Cost of a Data Breach Report 2021,’ the year 2021 saw the highest average cost of a data breach in 17 years, with the cost rising from USD 3.86 million to USD 4.24 million on an annual basis.
The rising frequency of cyberattacks and the higher number of compromised networks, apps, records, etc., indicate the severeness of risk posed by cyberattacks worldwide. Today, it has become essential for all businesses to adopt cyber security measures to keep them free from threats and vulnerabilities.
Why do businesses need to adopt cyber security measures?
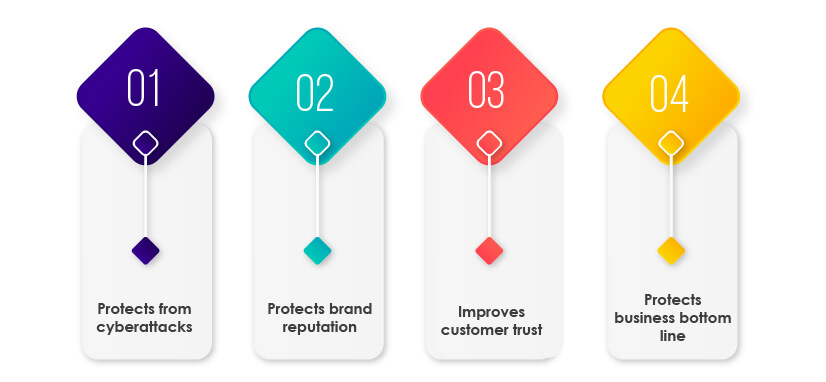
Protects from cyberattacks
The rapidly rising cases of cyberattacks have necessitated the adoption of robust cyber security measures. For businesses to protect their critical apps, systems, networks, and data from cyberattacks, the adoption of stringent cyber security measures is essential.
Protects brand reputation:
Cyber attacks pose a significant risk to the sensitive information of businesses and their customers. Any data leak can cause damage to their brand reputation. Therefore, businesses need to adopt effective cyber security practices.
Improves customer trust
Businesses need to protect customer data from cyber threats, as any loss of customer data can affect customer trust. Therefore, businesses need to adopt cyber security measures to improve customer trust.
Protects business bottom line:
Cyberattacks, especially ransomware, can cause great monetary loss to businesses. Hence, businesses need to protect themselves from ransomware and other cyberattacks to protect their business bottom line.
How can businesses protect themselves from cyberattacks?

There are various cyber security measures that businesses can adopt and leverage to ensure their apps, systems, infrastructure, and networks are free from threats and vulnerabilities. Some of them include:
Data encryption:
Businesses should ensure end-to-end data encryption of sensitive and critical data. Data encryption converts the data into a secret code and reduces the risk of cyber threats, data destruction, or data tampering.
Data backup:
Businesses need to keep their data backup to ensure easy recovery if the data gets lost due to a cyberattack.
Multi-factor Authentication (MFA):
MFA is a great way to protect businesses from any cyberattacks. MFA is a security verification process that requires the user to provide two or more additional proofs of identity to access the account. This way, MFA adds a layer of security and safeguards businesses from cyber threats.
Employee awareness:
Businesses should create awareness among their employees about cyber security policies and employ the best practices to keep their businesses safe from cyberattacks. Businesses should make their employees aware of the importance of strong passwords, secure downloads, anti-virus, etc.
Outsource security testing:
Outsourcing is when a company hires a third party to handle operations or provide services. Thus, businesses can outsource the security testing of apps, systems, and networks to an able outsourcing partner to get an unbiased opinion on the cyber security readiness of their business.
What is the need for outsourcing cyber security testing in 2022?
Rampant cyber attacks have increased the need for security testing of business-critical apps, networks, data, and more. This testing method involves an in-depth analysis of the business’ IT infrastructure from an attacker’s perspective to ensure no security loophole is left behind. Typically, it is beneficial for businesses to outsource their cyber security testing to an able security and vulnerability testing services provider, which ensures many benefits of saving time, costs, and more. Also, for businesses, maintaining a team of security QA experts and paying licenses for various security test automation tools involves some costs.
Some of the major benefits of outsourcing your cyber security testing include:
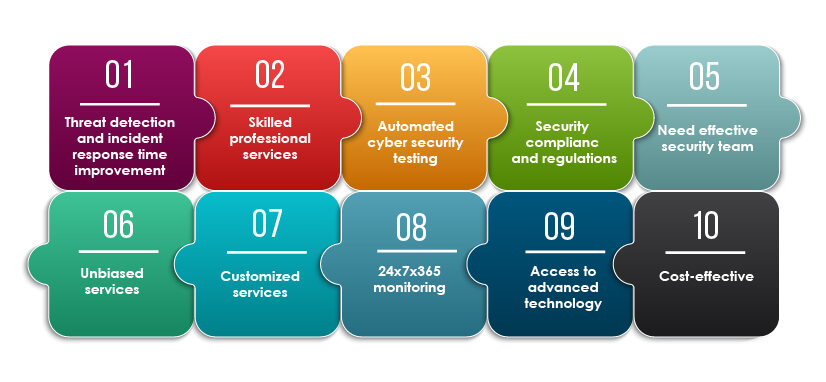
Threat detection and incident response time improvement:
One of the major benefits of outsourcing is the quick incident response time or turnaround time. With outsourcing, the services are available on time and much faster than in-house teams.
Skilled professional services:
Outsourcing security testing allows businesses to test their software with highly-skilled resources. The organizations that offer outsourcing services have skilled and certified experts that can help businesses improve their cyber security readiness.
Automated cyber security testing:
For in-house teams, it is challenging to source and keep a wide range of tools in-house. However, outsourcing partners have access to various tools and frameworks that they leverage to automate software testing.
Security compliance and regulations:
There are various types of compliances and regulations, such as HIPPA, GDPR, SOC, etc., that businesses should follow. Businesses can get their security compliance and regulations checked by outsourcing cyber security testing.
Need effective security teams:
Vulnerability testing is a complex and continuous task that keeps getting more difficult as the application grows. Usually, organizations have a limited workforce available who are involved in various activities. Therefore, it is better to outsource cyber security testing to security testing service providers with in-house security testing experts.
Unbiased services:
Reliable outsourcing partner provides unbiased opinions about the security readiness of a business. This helps business decision-makers make correct and unbiased decisions.
Customized services:
As the application grows, software testing becomes complex. Also, applications need to be tested more frequently and thoroughly during peak load days. With outsourcing, businesses can get customized services as per their needs.
24x7x365 monitoring:
With outsourcing, businesses can achieve 24/7 monitoring of their applications and faster response to their needs. It becomes easy to get seamless support from the outsourcing company.
Access to advanced technology:
A reliable outsourcing partner stays updated with the latest technological stacks, such as AI, ML, IoT, RPA, etc. By outsourcing cyber security testing, businesses can get their software thoroughly tested with the help of advanced technologies.
Cost-effective:
For a business, in-house hiring resources, upskilling them, and buying tools could be a costly affair. However, with outsourcing, businesses get skilled resources, advanced tools, customized services, and more at a much lower cost.
How to choose your outsourcing partner for cyber security testing?

Reputation in the market:
The outsourcing partner’s credibility and importance matter a lot. Before offering the project to the partner, the background, history, and market reputation should be checked.
Years of expertise:
Before choosing an outsourcing partner, it is essential to look at the experience level of the partner, years of service in the industry, clients served, client-communication procedures used by the partner, etc.
Automation capabilities:
Automation testing has become the need of an hour. Thus, before outsourcing security testing, ensure that the partner has relevant automation testing capabilities.
Service flexibility:
Every business has different security testing needs. An outsourcing partner should be flexible enough to cater to varying types of testing needs as per the requirement of the business.
Engagement models:
For businesses to choose a reliable outsourcing partner, it is essential to look at the engagement models, like project-based, managed, staffing/time & material, etc.,
Thought leadership:
Outsourcing partner’s proficiency and subject matter expertise should be checked before hiring. The thought leadership of the outsourcing partner is all that matters and should be looked upon before hiring them for the projects.
Authentic partners:
The authenticity of the outsourcing partner should be validated before hiring them for the software testing project. Customer references can be checked to validate their authenticity.
Budget-friendly:
The outsourcing partner should be budget-friendly and must fit into the budgetary limits of a business.
Conclusion
Undoubtedly, cyberattacks have been on the rampage and pose a great risk to business apps, data, systems, and networks and are at risk of losing customer trust and the organization’s reputation. Today’s businesses should ensure robust cyber security readiness by leveraging end-to-end security testing. Businesses should outsource security testing to the best outsourcing partner to protect their businesses from cyberattacks and ensure vulnerability-free. Outsourcing cyber security testing can help businesses achieve faster incident response time, save high costs, and overcome cyber threats and vulnerabilities.
How can TestingXperts help?

TestingXperts (Tx), is next gen specialist QA & software testing company, has been helping clients with a range of security testing needs. Our team of Certified Ethical Hackers (CEHs) ensures that your application is secure from vulnerabilities and meets the stated security requirements, such as confidentiality, authorization, authentication, availability, and integrity. Teams have more than ten years of expertise in assessing a wide range of applications for security threats and ensuring rigorous application testing for all possible threats and vulnerabilities.
Our Differentiators:
• A large pool of Certified Ethical Hackers (CEHs) with years of expertise in delivering security testing services to clients across domains
• Flexible engagement models best suited to customer’s business need
• In-house security testing accelerator Tx-Secure makes the security testing process quick seamless and helps you achieve significant results
• Secure and well-equipped in-house security testing labs help perform effective security testing of all applications, including Blockchain, IoT, network infrastructure, etc.
• Security testing services have conformance with International standards, such as GDPR, HIPAA, PCI-DSS, OSSTMM, OWASP, and others,
• Deliver detailed test reports to stakeholders to make informed decisions
• Ensure 24x7x365 seamless customer support
Discover more
Get in Touch
Stay Updated
Subscribe for more info